Data Science
Watch It
Discover Categories

Blockchain

Analytics
Big Data

Business Intelligence
Latest from SmartData Collective
AI Is Transforming EDI Compliance Services
Smart Data Collective is starting to explore how EDI compliance services are relying on AI more than ever to manage growing data demands. You can see that businesses are turning…
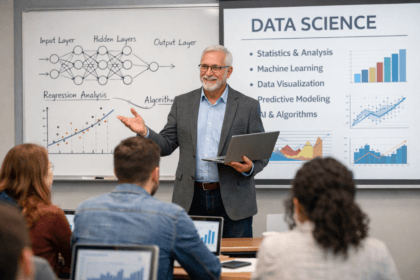
5 Industries Driving Big Data Technology Growth
Something that we have written a lot about on the Smart Data Collective blog is how different industries are driving…
California AI Companies That Are Set for Long-Term Growth
AI technology is changing our lives faster than ever. This is one of the things that we have written about…
The Power of Warm-Ups: Setting the Stage for Learning
There are a lot of things that we have talked about in Smart Data Collective over the years. One of…
Can Data Analytics Help Investors Outperform Warren Buffett
We write a lot about financial analytics in the Smart Data Collective blog. Something that continues to spark debate is whether data-driven strategies can truly rival the long-term success of…
Machine Learning Is Changing iGaming Software Development
Since Ryan took over as the lead editor at Smart Data Collective, we have examined how data analytics and AI…
Signals In The Noise: Using Media Monitoring To Manage Negative Publicity
Negative publicity can spread quickly across digital channels. News articles, blog posts, social media discussions, and customer reviews can shape…
Turning Dead Zones Into Data-Driven Opportunities In Retail Spaces
Retail stores often contain areas that receive far less customer attention than others. These low traffic zones can appear near…
Sign in to your account